The educational sector is increasingly reliant on technology for teaching, learning, and administration.
This shift, while beneficial, exposes educational institutions to a myriad of vulnerabilities, ranging from data breaches to unauthorized access to sensitive information.
Vulnerability management, the systematic approach to identifying, assessing, and addressing security weaknesses, is therefore critical in safeguarding educational environments against potential threats.
This article explores the concept of vulnerability management within educational settings, highlighting its importance, challenges, and best practices.
Understanding Vulnerabilities in Educational Environments
Vulnerabilities in educational environments can be broadly classified into three categories: physical, digital, and human-related.
- Physical vulnerabilities may include unsecured access points to buildings.
- Digital vulnerabilities involve weaknesses in software or networks that can be exploited by cyberattacks.
- Human-related vulnerabilities often stem from inadequate training or awareness regarding security protocols.
Examples of common vulnerabilities include weak passwords, outdated software, and the lack of encryption for sensitive data.
The Importance of Vulnerability Management in Education
Effective vulnerability management is vital in educational environments for several reasons:
- Protecting student data and privacy: With institutions holding vast amounts of personal information, ensuring its security is paramount.
- Ensuring uninterrupted educational processes: Cybersecurity incidents can disrupt teaching and learning activities, causing significant downtime.
- Compliance with legal and regulatory standards: Many regions have strict data protection laws that educational institutions must adhere to.
Steps in the Vulnerability Management Process
The vulnerability management process involves several key steps:
- Identification of vulnerabilities: Utilizing tools and techniques to scan for weaknesses within the system.
- Assessment and prioritization: Evaluating the severity of identified vulnerabilities and determining their priority for remediation.
- Remediation or mitigation strategies: Implementing solutions to fix vulnerabilities or mitigate their potential impact.
- Continuous monitoring and review: Regularly reviewing the security posture to identify new vulnerabilities and assess the effectiveness of implemented measures.
Challenges in Implementing Vulnerability Management
Educational institutions face several challenges in implementing effective vulnerability management, including limited financial and human resources, the constantly evolving nature of cybersecurity threats, and the need to balance security measures with the accessibility of educational resources.
Best Practices and Recommendations
To overcome these challenges, educational environments can adopt the following best practices:
-
Regular training and awareness programs for staff and students to recognize and prevent security threats.
-
Adoption of industry-standard tools and protocols to ensure a robust security infrastructure.
-
Collaboration with cybersecurity experts to stay updated on the latest threats and mitigation techniques.
Conclusion
Vulnerability management plays a crucial role in protecting educational environments from security threats.
By understanding vulnerabilities, implementing a systematic management process, and adopting best practices, educational institutions can significantly enhance their security posture.
Encouraging proactive measures and continuous improvement will help safeguard the future of education in the digital age.
Educational institutions are treasure troves of sensitive data, making them prime targets for cyber threats.
In 2023, the education sector faced significant financial losses due to cybersecurity vulnerabilities. The average cost of a data breach in the education sector was reported to be $3.65 million. Additionally, the median recovery cost in lower education was $750,000. These figures underscore the substantial financial impact that cybersecurity incidents can have on educational institutions, highlighting the importance of robust vulnerability management and cybersecurity measures
With Inspiroz Cybersecurity, you can shield your institution from the myriad vulnerabilities that threaten the sanctity of educational processes and the privacy of student data.
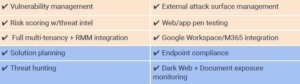
Our Comprehensive Suite of Services Includes:
Why Inspiroz Cybersecurity?
With Inspiroz Cybersecurity, you’re not just getting a service provider; you’re gaining a partner committed to the safety and security of your educational institution.
Our comprehensive suite of services is designed to address the unique cybersecurity challenges faced by educational environments, ensuring your data is protected, your operations are uninterrupted, and you remain compliant with legal and regulatory standards.
Take Action Now.
Don’t wait for a cybersecurity incident to disrupt your educational processes or compromise student data.
Contact Inspiroz Cybersecurity today to learn how we can help safeguard the future of your institution in the digital age.
Take a Free Assessment of Your Cybersecurity Posture
At Inspiroz Cybersecurity, we understand the importance of knowing where you stand in terms of cybersecurity.
That’s why we’re offering a Free Assessment of Your Cybersecurity Posture.
This no-obligation assessment will give you a clear understanding of your current security strengths and areas for improvement.